Cite this document
(“Develop a questionnaire and analyse the data Essay”, n.d.)
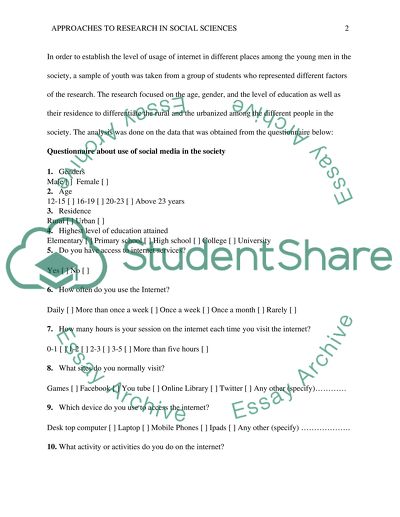
Develop a questionnaire and analyse the data Essay. Retrieved from https://studentshare.org/sociology/1484849-develop-a-questionnaire-and-analyse-the-data
Develop a questionnaire and analyse the data Essay. Retrieved from https://studentshare.org/sociology/1484849-develop-a-questionnaire-and-analyse-the-data
(Develop a Questionnaire and Analyse the Data Essay)
Develop a Questionnaire and Analyse the Data Essay. https://studentshare.org/sociology/1484849-develop-a-questionnaire-and-analyse-the-data.
Develop a Questionnaire and Analyse the Data Essay. https://studentshare.org/sociology/1484849-develop-a-questionnaire-and-analyse-the-data.
“Develop a Questionnaire and Analyse the Data Essay”, n.d. https://studentshare.org/sociology/1484849-develop-a-questionnaire-and-analyse-the-data.